What is Malware?
Malware, short for malicious software, refers to any intrusive software developed by cybercriminals (often called hackers) to steal data and damage or destroy computers and computer systems.
Signs You may have Malware
If your computer has malware, it may react accordingly:
- Become unexpectedly and increasingly slow
- Take longer to load applications
- Get stuck on applications or web pages
- Shut down unexpectedly
- Display error messages continuously
- Display a lot of ads while you browse the internet
- Not open your task manager or activity manager
- Not allow programs to uninstall
- Shows new and unexpected toolbars or icons in your browser or on your desktop
- Uses a new default search engine, or displays new tabs or websites you didn’t open
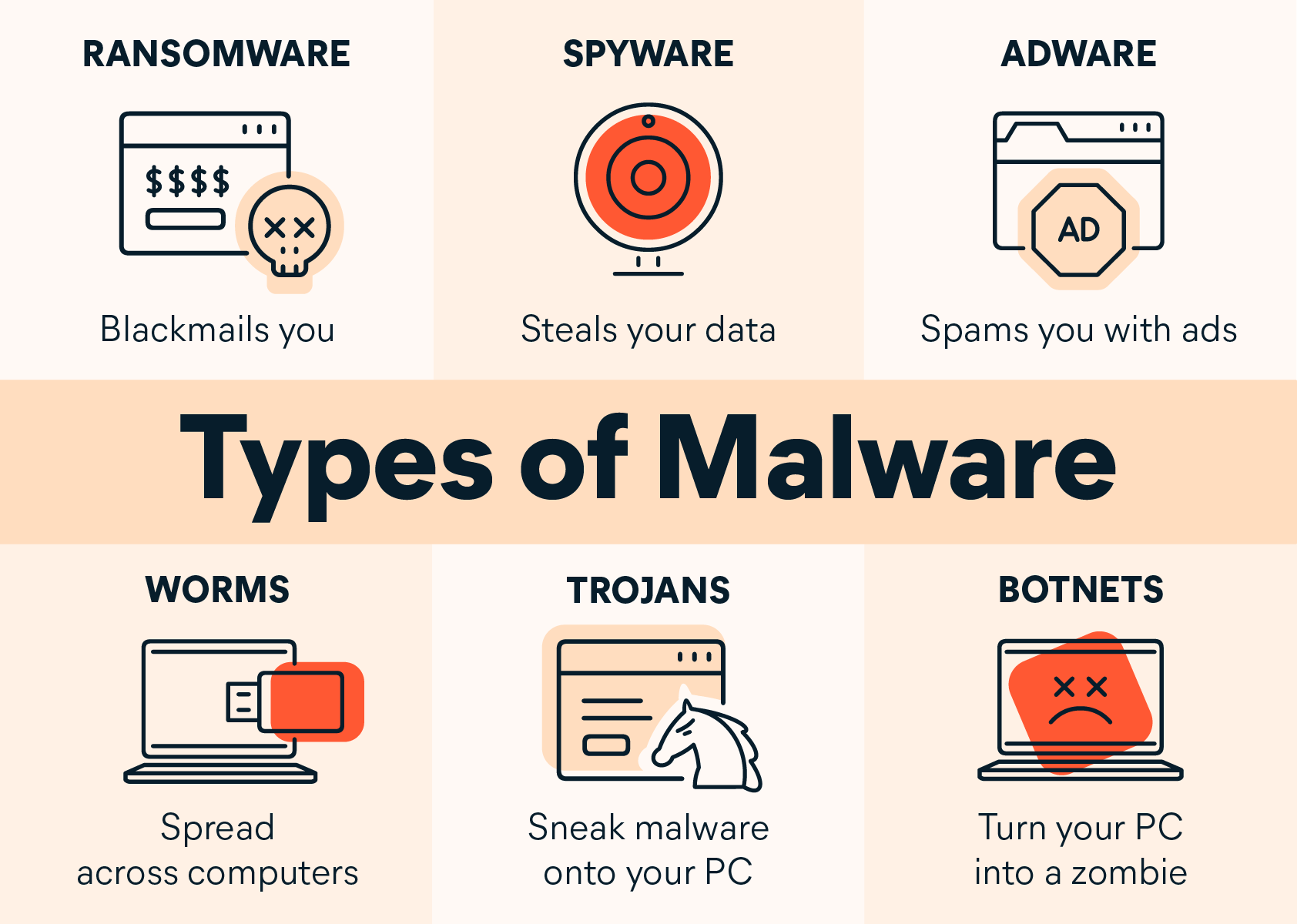
Types of Malware
Ransomware
Ransomware encrypts a computer's data so that it is inaccessible without a password. The ransomware distributor will then demand a certain amount of money, sent through an anonymous method like bitcoin, in order to decrypt the computer. There is sometimes a time limitation for payment. After this time limit, the computer's files will be deleted. The best way to recover from ransomware is to recover your data from a backup.
Spyware
Spyware will record activity on your computer and transmit the data elsewhere. This includes login information, browser history, and potentially other information. Spyware will try to remain hidden so that it won't be removed. It can also modify security and network settings.
Adware
Adware is essentially abusive advertising. This includes pop-up ads and "bundled" software such as browser toolbars. Some adware is innocuous advertising, but other instances of adware can potentially damage your computer or steal your information. It is never a good idea to knowingly install or click on adware. When downloading software, be sure it is not also asking permission to download additional software on top of the desired product and when browsing be sure to use pop-up blockers or script blockers.
Worms
Worms are spread through networks, finding security vulnerabilities in programs and operating systems to infect machines. They can damage your computer, steal or delete information, and install bots.
Trojan Horse
A Trojan Horse will trick a user into downloading malicious software. These programs will pretend to be something else that you are trying to download, but instead will give someone else access to your computer to steal information and install additional malware.
Rootkit
Rootkits allow access to sensitive files that usually are not modified by computer users - at least not directly. Rootkits can include viruses, worms, and Trojan horses. These programs will modify the computer, steal personal information, execute malicious files, and potentially create bots. Rootkits, unlike adware and ransomware, will typically attempt to stay hidden from the user.
Virus
Viruses are malicious programs that will attempt to spread from machine to machine. They can attach themselves to files and programs shared between computers in order to infect as many machines as possible.
Best Practices
- Updated software: Cyber criminals target older versions of software when they create malware. Keep your software updated, as updates will address security flaws and stability and usability issues. Install the latest security features.
-
Anti-Virus Software: Use anti-malware software. For University-owned devices please call the Service Center at 661-654-4357 or submit a ServiceNow ticket. They will assist with enrolling your device in SentinelOne for Windows and JAMF for MacOS, if your device doesn't already have it. For non-CSUB devices, Malware Bytes is the recommended and free anti-virus software.
- Browser Extensions: Browser extensions help with protecting your privacy. Extensions can help block you
from malicious ads and malware, inform you about a website, block scripts, and enforce
SSL.
Resources: - Encrypted Browsing: Only send personal information to websites you know are fully encrypted (the "https:" before the webpage's URL address).
- Enable Firewall: Make sure that Windows Firewall is enabled to block viruses, worms, and hackers.
- Use Multi-Factor Authentication (MFA): Use Duo multi-factor authentication so that even if your password is stolen from public Wi-Fi, a second factor is needed.
- Open Email Attachments with Caution: Be wary of opening email attachments, even from senders you think you know, particularly when attachments are compressed files or ZIP files. Refer to our Phishing Protection page for more information.
- Verify Email Senders: If you are unsure whether or not an email is legitimate, try to verify the email’s legitimacy by contacting the sender directly.
- Inform Yourself: Keep yourself informed about recent cybersecurity threats and up to date on ransomware techniques. You can find information about known phishing attacks here:
Office of Information Security
InformationSecurity@csub.edu
(661) 654-3425
Doug Cornell
Information Security Officer
dcornell@csub.edu
(661) 654-3474
Office: LIB ITV2C
Return to Information Security Home